Collecting information online has become normal for businesses of all sizes. From customer feedback to employee records, companies depend on structured forms to gather and manage information safely. But while digital systems are convenient, security must always come first.
If an online form is not properly protected, sensitive details like names, emails, and health data can be exposed. That is why building a secure system from the beginning is essential.
A data collection form is simply a structured way to gather information. It can be used for registrations, surveys, support requests, or internal processes. However, without the right protections in place, even a simple collection form can create risk.
In this guide, we will explain common security concerns, outline basic compliance standards, and show practical steps you can take to protect your data.
Why Security Matters in Online Forms
Every time someone fills out an online form, they trust your business with their information. If that information is leaked or misused, it can damage your reputation and lead to legal consequences.
Common risks include:
- Data breaches caused by weak passwords
- Unauthorized access from internal teams
- Insecure storage systems
- Unencrypted transfers of data
Security should not be an afterthought. It should be part of your overall data collection strategy. Whether you are collecting customer emails or employee records, protection is critical.
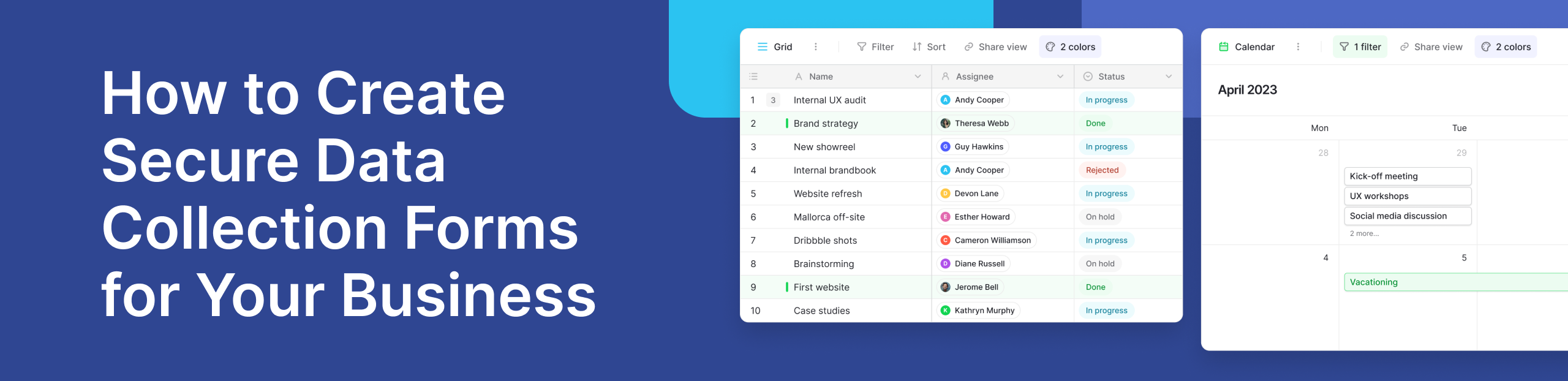
Modern platforms now offer built-in safeguards that reduce these risks. Instead of storing information in scattered spreadsheets, businesses are moving toward structured, database-backed systems.
Understanding GDPR and HIPAA Basics
Two important regulations businesses often hear about are GDPR and HIPAA.
GDPR (General Data Protection Regulation) applies to businesses that handle personal data of people in the European Union. It requires clear consent, data transparency, and strong protection measures. You can learn more in this helpful guide.
HIPAA (Health Insurance Portability and Accountability Act) focuses on protecting medical and health-related information in the United States. If your organization handles health data, compliance is mandatory.
Even if these regulations do not directly apply to your company, following their principles is a good practice. They promote secure storage, controlled access, and responsible data handling.
Role-Based Permissions and Access Control
Not everyone in a company should see all collected information.
Role-based permissions allow businesses to control who can view, edit, or manage specific data. For example, HR staff may need access to employee records, but marketing teams do not.
Limiting access reduces the risk of accidental exposure. It also creates accountability. Audit logs help track who accessed or changed information, which improves transparency.
If you want to understand how permissions improve security, this guide explains it clearly.
Platforms like Baserow also provide dedicated security features, including role-based access controls and structured permissions management. You can review their security overview here.
These features help businesses maintain full data control without needing complex technical setups.
Choosing the Right Secure Form System
When selecting a secure system, consider the following:
- Encrypted data transmission
- Secure storage infrastructure
- Role-based access control
- Audit logs for tracking changes
- Option for self-hosting when required
Self-hosting gives organizations greater control over where their information is stored. This is especially important for businesses handling sensitive records.
A structured form template connected directly to a database ensures that responses are organized and secure. Instead of saving files locally or sending them by email, modern systems centralize information in one protected environment.
If you are evaluating secure options, explore the form builder solution.
To better understand broader approaches to collecting information, read our detailed guide on data collection methods.
Simple Security Checklist Before You Publish a Form
Before making any form live, review this checklist:
- Use HTTPS encryption
- Limit user permissions
- Enable audit tracking
- Store responses in secure databases
- Review compliance requirements
- Test your form before launch
Following these steps makes your online form safer and more reliable.
Conclusion
Creating secure systems does not have to be complicated. By focusing on compliance, access control, encryption, and structured storage, businesses can confidently collect information online.
Modern tools make it easier to centralize records, manage permissions, and maintain full visibility over data.
Build secure forms with Baserow and simplify your digital workflows today.
Baserow 2.2 introduces AI app building with Kuma, view-level permissions, edit rows via forms, and more. Explore all updates.

Discover how Airtable and Baserow compare in features, flexibility, speed, and scalability. Compare pricing plans and hidden costs to make an informed decision!

Explore the best open-source software alternatives to proprietary products. Discover OSS tools, licenses, and use cases with our updated directory.
