Ensuring the right people have the right access is the cornerstone of effective data protection. As organizations scale, moving beyond simple spreadsheets to robust database tools requires a sophisticated security layer.
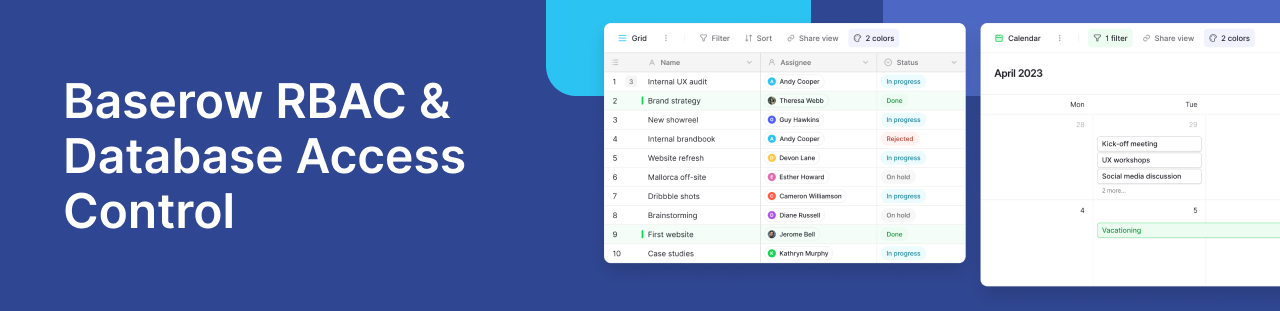
If you are migrating from tools that only offer basic “view” or “edit” toggles, you likely need a more powerful system for controlling access. Baserow provides this through a flexible permissions hierarchy, ranging from basic workspace sharing to granular Role-Based Access Control (RBAC).
Whether you are managing customer data, internal business processes, or complex data flows, understanding how to restrict access and implement strict data governance rules is vital for protecting your organization.
Why basic spreadsheet permissions fail as you scale
At its core, Baserow is designed to reduce the risk of unauthorized data exposure. While small teams might start with basic roles, growing enterprises quickly hit a wall when they need to protect sensitive information like HR records or financial statements without locking down the entire database.
For teams on Free or Premium plans, permissions are straightforward: you are either an Admin (full control) or a Member (full data access). However, as your operations grow, the user experience demands more nuance.
The Advanced and Enterprise plans introduce true Role-Based Access Control, allowing you to assign specific, custom permissions that dictate exactly how team members interact with your management system.
How to implement granular access control across your workspace
The beauty of Baserow’s RBAC lies in its hierarchy. You can set a baseline rule at the workspace level and then define stricter, granular controls as you drill down into specific databases, tables, fields, or views.
- **Workspace Level:** The broad starting point. Establish baseline permissions for all team members.
- **Database Level:** Ideal for department-specific access. (e.g., Allow the Marketing team to edit the Content database, but only view the Finance database).
- **Table Level:** A higher level of granular security, where you can restrict access to specific sets of data within a shared department.
How to hide sensitive columns with field-level security
Roles define who can see a table, but what if you need a user to update a client’s status without seeing their billing information? Field-level security and field permissions ensure that specific columns, like social security numbers or private API keys, remain hidden or uneditable, even from team members who have general access to the table. This is especially important when setting up external data entry, ensuring users only see what they strictly need.
Securing API integrations and data flows
For developers, permissions are just as critical programmatically as they are visually. Every Baserow API request is governed by the same RBAC rules as the web interface. Whether you are using REST APIs to exchange data with third-party tools or setting up a complex automation, your integration remains secure.
By limiting access via specific tokens and roles, you ensure that your organization’s data remains protected even when accessed by external applications.
Access the complete API specification:
- Interactive docs: https://api.baserow.io/api/redoc/
- JSON schema: https://api.baserow.io/api/schema.json
Best practices for strict data governance
To maintain a secure environment as you scale, consider these strategies:
- Use Teams: Instead of manually managing individuals, use role-based access control at the team level (e.g., “Freelancers” or “Managers”) to drastically reduce system overhead.
- The “No Role” Strategy: For a zero-trust model, assign “No Role” at the workspace level and explicitly grant access only to specific databases as needed.
- Regular Audits: Perform regular audits of user permissions to ensure no “permission creep” occurs as staff change roles or leave the company.
Frequently asked questions about database permissions
How do I restrict access to specific columns or hide sensitive fields from my team?
Unlike basic spreadsheets where you might have to create a separate file to hide data, Baserow uses field permissions. This allows admins to define exactly who can view or edit specific fields (columns) within a table, adding a security layer that protects sensitive data from team members who otherwise have access to the record.
Can I restrict what third-party apps can do with the Baserow API?
Yes. Every API request requires an API token, and the permissions associated with that token are strictly tied to the user’s role. This ensures granular control over how external applications and integrations view or exchange data with your databases.
What is the difference between “No Access” and “No Role” in Baserow?
“No Role” means the user has no default permissions in that specific area and must be granted them via a team or higher-level setting. “No Access” is an explicit, strict block used to restrict access completely, overriding any permissions a user might normally inherit from a higher level.
Can I use Baserow to store data if I need HIPAA or GDPR compliance?
Absolutely. By utilizing our granular access controls, data encryption, and self-hosted deployment options, Baserow provides the infrastructure necessary for organizations to meet strict data protection and residency standards like GDPR and HIPAA.
For more technical details, visit the Baserow Documentation.
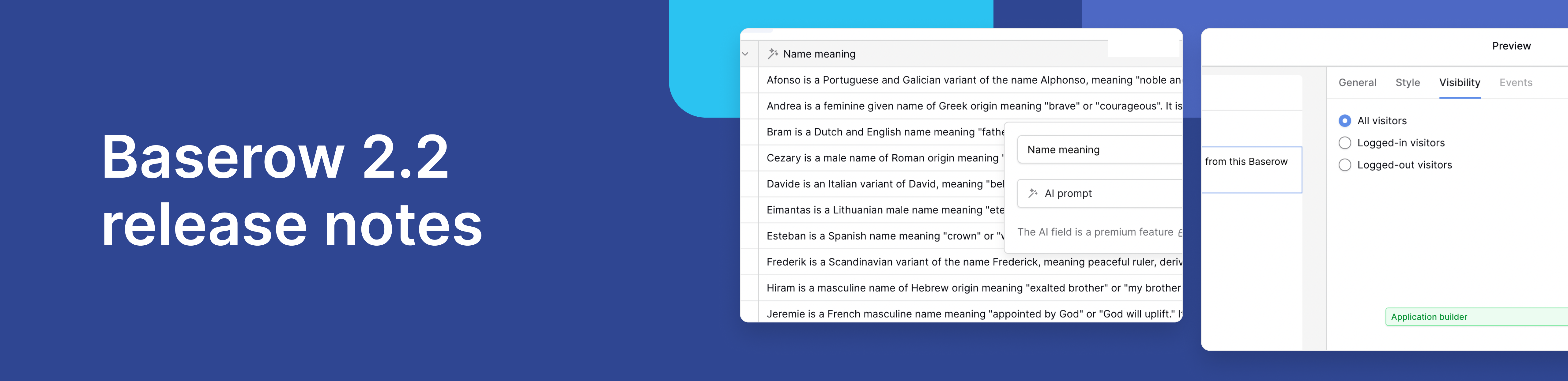
Baserow 2.2 introduces AI app building with Kuma, view-level permissions, edit rows via forms, and more. Explore all updates.

Discover how Airtable and Baserow compare in features, flexibility, speed, and scalability. Compare pricing plans and hidden costs to make an informed decision!

Explore the best open-source software alternatives to proprietary products. Discover OSS tools, licenses, and use cases with our updated directory.
